Vulnerability disclosure - Ethical Hacking
Responsible vs Full vulnerability disclosure
The never ending debate
Software and hardware vulnerabilities are found every day, this means that especially we, users, are under the constant risk of losing the most important asset we have today, information. Cyber Security vulnerabilities are weaknesses and flaws in computer systems, they can be of many different types and can be exploited in many different ways, ultimately exposing the system to external, probably malicious, threats. Vulnerabilities can aim to take down systems availability, ex-filtrate credentials, user data, secrets documents and much more.
Security has been underrated by a large number of companies and SW houses for quite a while, it is mainly thanks to the more sensitization that in the recent years more focus has started to been put into applying better security policies and best practices. Although the main problem is that absolute security is hard if not impossible to achieve, it is costly, it is broad and it is complex to implement requiring deep technical knowledge.
Security is also taught to be as a “process”, in fact, following a structured way, adopting the correct mindset, from the various stages of planning and design to the multiple stages of implementation and testing is one of the best ways to decrease risks for businesses and users.
The Secure Software Development Life Cycle (SDLC) is an example of such a framework that “help discover and reduce vulnerabilities early, effectively building security in it” [1]. Unfortunately, it is very easy for programmers to make errors, and those commonly turn out as vulnerabilities, found by hackers and bug hunters for example. Bulletins, CERTs, forums, mailing lists and social media are the most used means for vulnerability reporting.
When it comes to vulnerabilities disclosure the topic is controversial in many ways that a clear solution is not easily pointed out. First of all, what are the types of vulnerability disclosure?
Mainly, who finds a vulnerability can usually go for three options: no disclosure, responsible disclosure and full disclosure. The last two are the most debated since they involve different course of action for the company who needs to fix the vulnerability. Every one of the two has different pros that are backed up by competent and respected people in the field.
The Responsible Disclosure
Responsible disclosure is essentially a way to give companies a chance to patch the security issue before the vulnerability is disclosed to the public. This involves an agreement between the two parties, in which on one side an amount of time is given to the company to fix the problem and on the other, the finder of the vulnerability agrees on not disclosing any details about it. Often it may require collaboration between the two to explain the issue and find the correct way of fixing it.
Responsible disclosure is often pointed out as the preferred “ethical way to go” because it avoids putting unexpectedly out into the wild the potential tools for attacking unpatched versions of the software. This involves that companies do want to know if there exists actual vulnerabilities in their software and are ready to take action and develop security updates.
Unfortunately that is not always the case, in fact, at times the “desire by organizations to know about their vulnerabilities is not always matched by a willingness to act on the information. This is one of the issues at the heart of the disclosure debate.” [2]
Sometimes companies can also threaten legal actions against researchers who find out vulnerabilities in their products, that is another aspect that leads to full disclosure, in fact, not every organization employs Bug Bounty programs which legally allows and stimulates researchers to find out bugs in production environments.
To let more researchers find vulnerabilities, organizations should establish easier responsible disclosure processes and create preferential channels for faster responses. That could be quite hard since all the security aspects do not bring direct benefits and income to the company, thus they tend to delay such matters.
On the other hand Travis Ormandy, the Google Project Zero researcher uncovered in September 2019 a security bug in the famous Lastpass password manager [3]. The bug could allow an attacker to ex-filtrate user’s previously used password from their browser. The responsible disclosure allowed Lastpass to immediately recover, fix the bug and roll the update making people safer before they even knew could be at risk.
The BlueKeep vulnerability reported by Microsoft on May 2019 is another case of responsible disclosure which helped the organization rolling out a security update before going public with all the details.
These are a good example of how useful and safe could the responsible disclosure be, even if the major problem remains the amount of outdated computers and applications still running.
Full disclosure
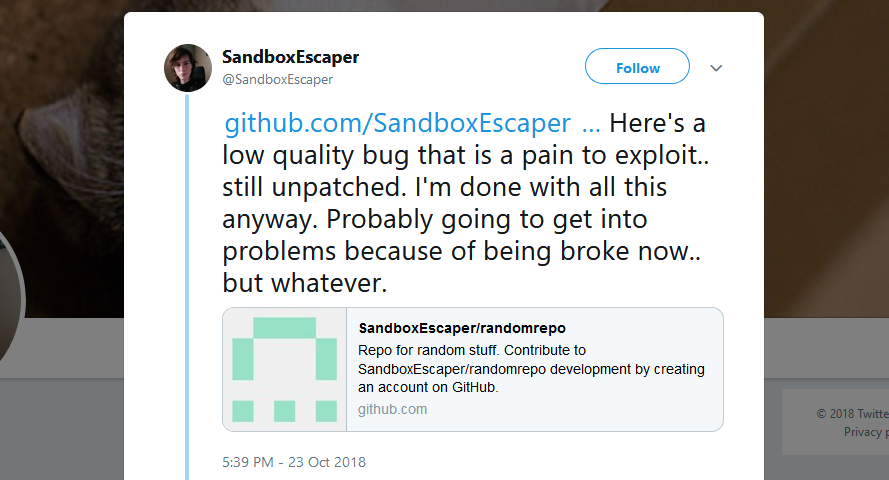
Full disclosure is on the other hand when someone discovers a vulnerability and without reporting it first to the organization, he publishes it on the Internet through social networks or mailing lists. The main intent of the researcher is to spur companies to act immediately and putting them in a potential disadvantageous situation helps to reach the goal. Furthermore, full disclosure will worsen the organization’s reputation and the only thing that can be done to get back is to fastly develop security updates.
This has multiple side effects, the company must now address the issue as soon as possible (is a good thing) but it is racing against attackers who want to develop a working exploit to take advantage of the unpatched systems.
This means the company is under bigger pressure but now is obliged to deal with it in the shortest time possible, which means there isn’t enough time to go thoroughly into the issue and a simpler workaround solution is the first thing to come up. That is a downside though, since quickest solutions are often the worse ones, and there is the risk to add other types of issues while trying to fix the previous one in the first place.
In fact, Mark Miller, director of Microsoft Security Response Center is pro responsible disclosure and points out that “responsible disclosure, while not perfect, doesn’t increase risk as full disclosure can. Generally, responsible disclosure benefits everyone involved by providing the best possible protection for customers without forcing vendors into sacrificing quality or security or introducing additional risk.” [4]
It is very common indeed that researchers alert the companies of actual vulnerabilities and that those companies do not answer at all, or even worse, as it happened to Troy Hunt, the same company’s Twitter page has blocked the researcher along with his tweets about an insecure direct object reference vulnerability discovery. The vulnerability allows an attacker to ex-filtrate data of each user registered on the website. [5] Troy also pointed out how difficult it has been to reach to organizations for vulnerabilities reporting. This aspect contributes to choose full disclosure.
On the other hand, another big example, this time in favour of responsible disclosure, was the one in 2017 of Meltdown and Spectre, hardware vulnerabilities in central processing units (CPU) that exploit the “speculative execution”, a feature designed to improve performance of modern Intel, AMD, and ARM processors. The vulnerabilities (dated back to as far as 1995) were critical and allowed an attacker to read memory from the secure kernel space. The researchers behind it understood that the immediate future impact of this vulnerability was catastrophic with full disclosure, allowing attackers to impact almost every desktop, server, cloud, mobile device around the world. [6] Researchers used the responsible disclosure and worked with the organizations to help mitigate the issues. After the patches were rolled out, they released the PoC exploit code. This is an example of how impact less could be a responsible disclosure instead of a full disclosure since the main interest is protecting the users
Although industry thought leaders like Bruce Schneier argues that full disclosure provokes an immediate urgent response from organizations that otherwise, very probably, would have taken the issue very lightly. [7]
It wasn’t until researchers published complete details of the vulnerabilities that the software companies started fixing them.
And about responsible disclosure Schneier says that “it remains a good idea only as long as full disclosure is the threat.” with which I agree with.
I think that responsible disclosure could be the right starting point, both ethically and consequences-wise, as soon as the company cooperates and fulfills his duty to quickly patch the vulnerabilities. In any other case, if the organization refuses to cooperate, or if the organization takes too much unmotivated time, the threat to go full disclosure is more than justified. If an individual wants to help the society and be ethical, the goal is to improve the general awareness and security of users, not to let big companies grow their profit without even trying to protect their first income source.
Another aspect to consider is that undisclosed vulnerabilities or zero days are worth huge amounts of money on the black markets. That is another factor that, ethic aside, could change a researcher’s mind. Prices for zero-days can easily go from $10'000 to $2'500'000 and more according to Zerodium [8] which is an exploit acquisition platform.
A different example was the big windows hacking tools leak from the NSA by the Shadow Brokers hacking group [9], in this case, ready and working exploits for zero-day vulnerabilities went directly public. This resulted in an important race in which hackers took advantage and developed different malware and ransomware based on the ready exploits. It is the example of the infamous Wannacry and Petya ransomware which caused several important damages to businesses and public services around the world. These ransom exploited the EthernalBlue vulnerability released in 2017 [10], Microsoft quickly developed security updates, but not every device gets updated immediately and so the ransomware campaign succeeded very well.
There seems to be no clear answer to the debate since the various motivations can be all seen with some level of agreement
Thanks for reading
/Carlo Alberto
References
- [1] https://dzone.com/articles/ssdlc-101-what-is-the-secure-software-development
- [2] https://www.csoonline.com/article/3259882/has-responsible-disclosure-won-the-debate.html
- [3] https://www.zdnet.com/article/lastpass-bug-leaks-credentials-from-previous-site/
- [4] https://www.csoonline.com/article/2121631/microsoft–responsible-vulnerability-disclosure-protects-users.html
- [5] https://www.troyhunt.com/kids-pass-just-reminded-us-how-hard-responsible-disclosure-is/
- [6] https://www.recordedfuture.com/meltdown-spectre-vulnerabilities/
- [7] https://www.schneier.com/blog/archives/2007/01/debating_full_d.html
- [8] https://zerodium.com/program.html
- [9] https://www.zdnet.com/article/shadow-brokers-latest-file-drop-shows-nsa-targeted-windows-pcs-banks/
- [10] https://www.zdnet.com/article/why-the-fixed-windows-eternalblue-exploit-wont-die/
